/ projects / kql-lab
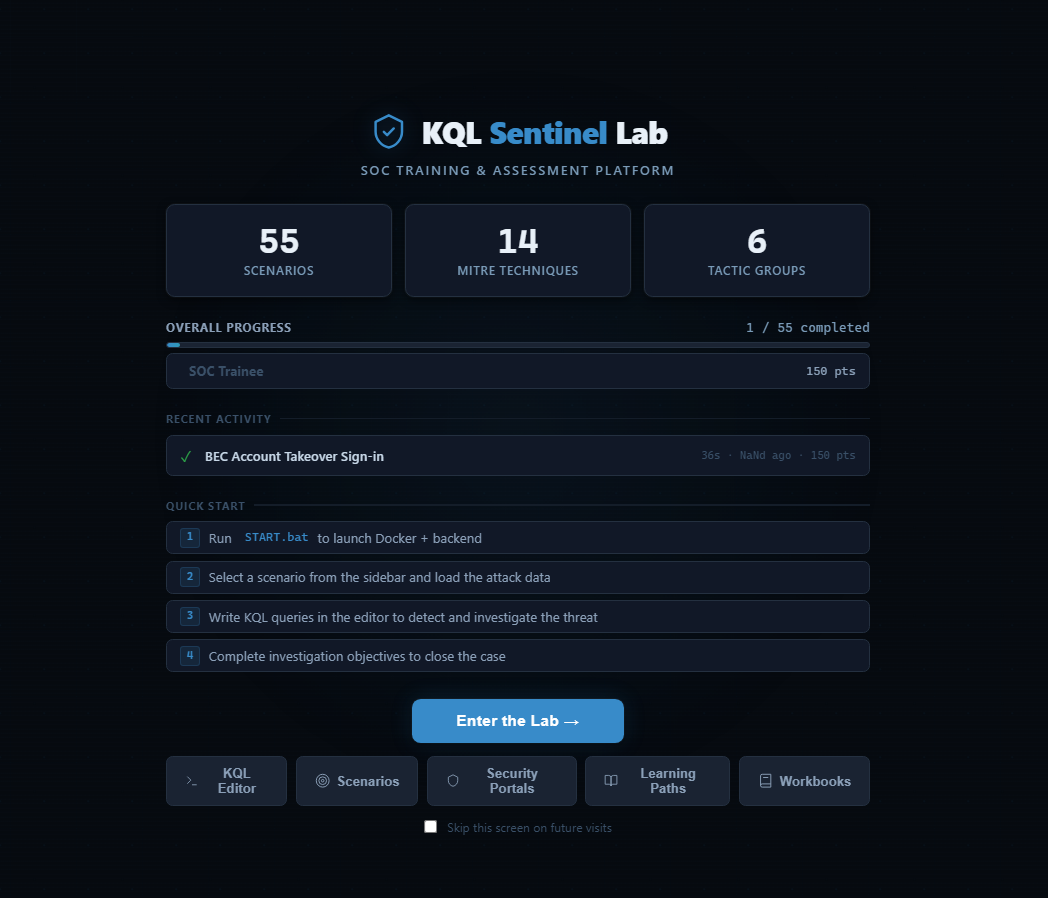
KQL Sentinel Lab
Synthetic Sentinel environment for analysts to practice on real attack data
Built into it
- Synthetic Sentinel data generator
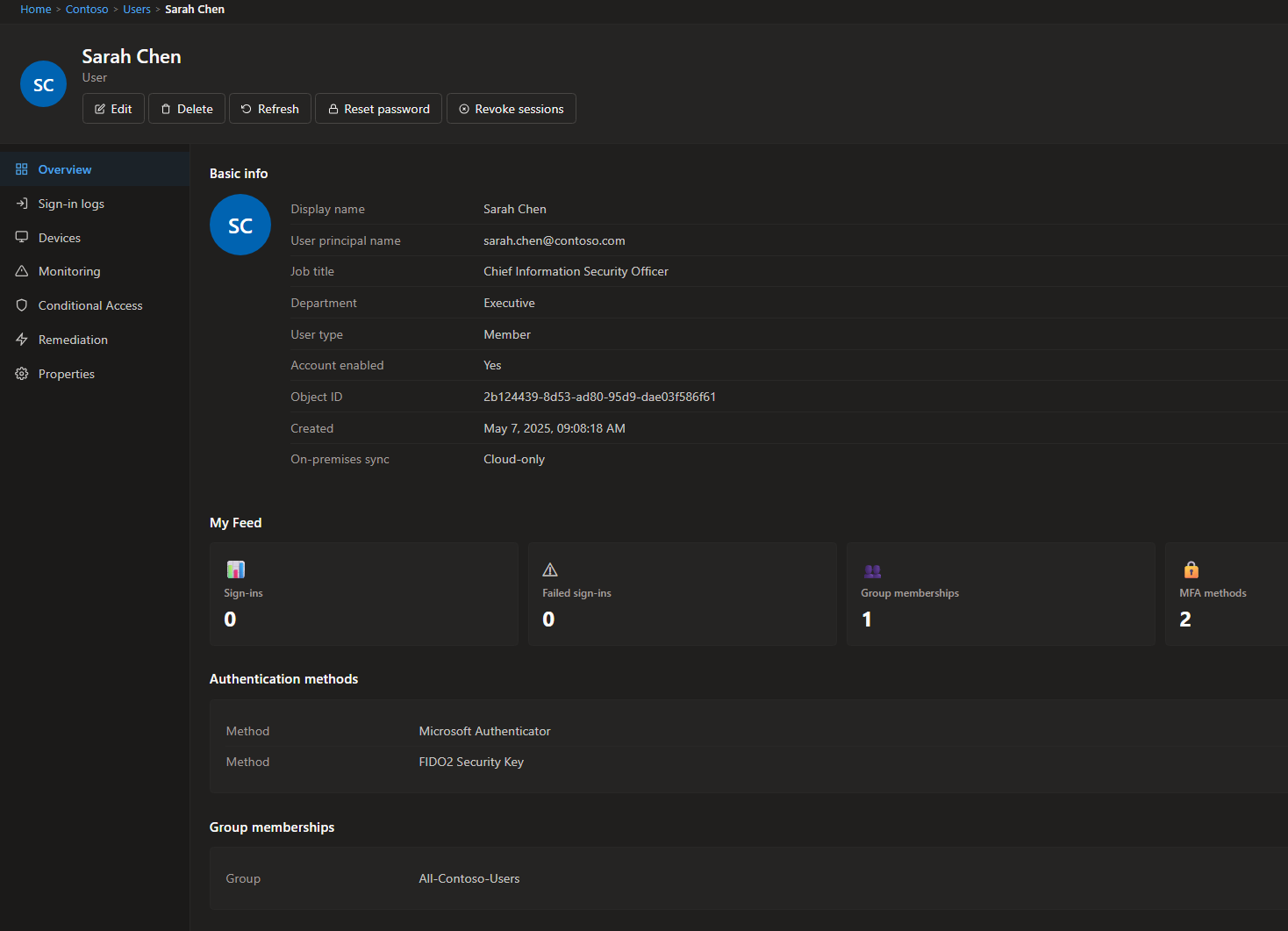
- Mock Entra ID + Defender XDR portals
- Severity + escalation workflow
Problem
Analysts learning KQL have nowhere safe to make mistakes. Production Sentinel workspaces hold sensitive data, so practice gets reduced to reading docs and running queries against thin demo datasets. The scenarios that actually matter — BEC, password spray, impossible travel — are hard to study without log patterns that look like the ones production alerts fire on.
Approach
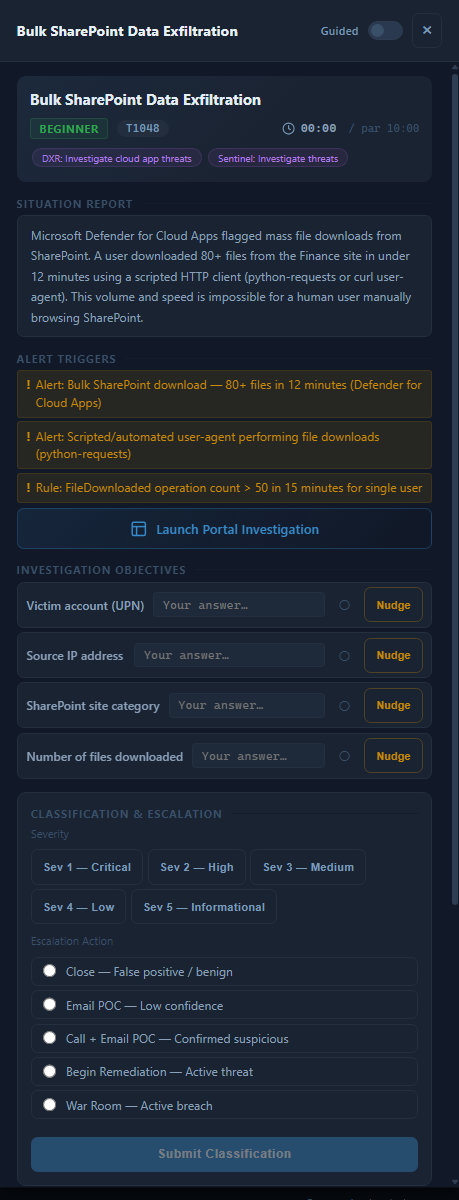
KQL Sentinel Lab gives analysts a synthetic Sentinel they can break. A FastAPI backend seeds 55 attack scenarios across the major MITRE ATT&CK categories with deterministic, realistic log rows in the core Sentinel schema tables. Analysts query the data through a Monaco-based KQL editor and check their findings against pre-generated expected answers. The whole environment spins up in one Docker command.
// Detecting impossible travel in generated scenario data
SigninLogs
| where UserPrincipalName == "[email protected]"
| where TimeGenerated > ago(2h)
| project TimeGenerated, Location, IPAddress, ResultType
| order by TimeGenerated asc
// Two successful logins from different continents within 40 minutes
// IPAddress: 198.51.100.10 (JP) then 10.1.2.3 (US VPN) — impossible gap
The frontend mirrors the Sentinel UI — VS Code-style sidebar, portal views for Entra ID and Defender XDR, an analytics rules wizard — so analysts build muscle memory on the actual interface, not an abstraction of it.
Each scenario opens with a situation report, the alert triggers that fired, and a set of investigation objectives the analyst fills out as they work. Severity classification and the close action — FP, email POC, war-room — are part of the workflow, same shape as the production close routine.
Outcome
New analysts get reps on production-shaped log structures before they touch a live workspace. The SC-200 practice exam and cert pathway cards add a structured progression next to the hands-on scenarios, which matters more than I expected — most people want to see the runway before they commit to running.
What’s next
More C2 and exfiltration scenarios are the current priority. The baseline normal-day scenario also needs more realistic noise variance — right now it’s too clean to teach the “is this anything?” instinct that production volume forces.
/ related · 03
Other projects
- 01
BASTION
KQL investigation toolkit that ends the rebuild-from-scratch loopHTML JavaScript Python FastAPIActive - 02
CARL
Offline SOC knowledge base that captures what lives in analysts' headsHTML JavaScript Python FastAPIActive - 03
ThreatWatch
Curated threat intel delivery from RSS feeds to Slack, automated dailyHTML JavaScript Python FastAPIActive